A new Quandela paper shows that secure delegated quantum computing can move closer to practical photonic hardware. The protocol allows the client to delegate computations without revealing them and testing that the server performs them correctly with information-theoretic composable security. The client only needs to send attenuated laser pulses to run the protocol while the server uses quantum emitters as both laser-to-qubit converters and entanglement generators, which drastically reduces hardware requirements on both sides compared to previous approaches.
Secure delegated quantum computing addresses one of the most important questions in quantum cloud computing: how can a user run a valuable quantum computation on a remote server without revealing the input, the algorithm, or the output to that server, and without simply trusting it to behave honestly? In the strongest versions of the problem, the user should also be able to check that the computation was carried out correctly. That is the promise of Secure Delegated Quantum Computation, or SDQC.
In a new paper published in Quantum “Towards practical secure delegated quantum computing with semi-classical light“, Quandela researchers propose a way to keep those strong security guarantees while making the hardware much more realistic. The core idea is simple and powerful: replace demanding client-side single-qubit hardware with weak laser pulses, then use quantum emitters on the server side to convert those pulses into the photonic resource states needed for blind and secure quantum computation.
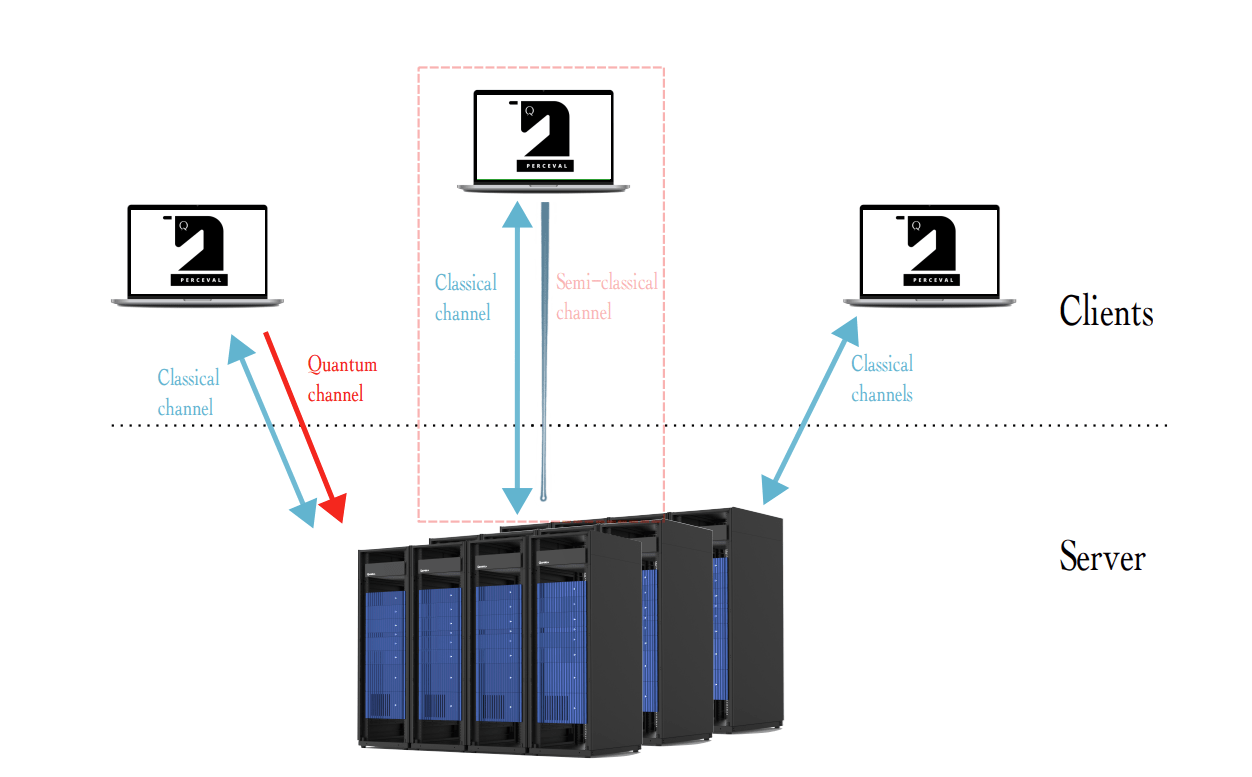
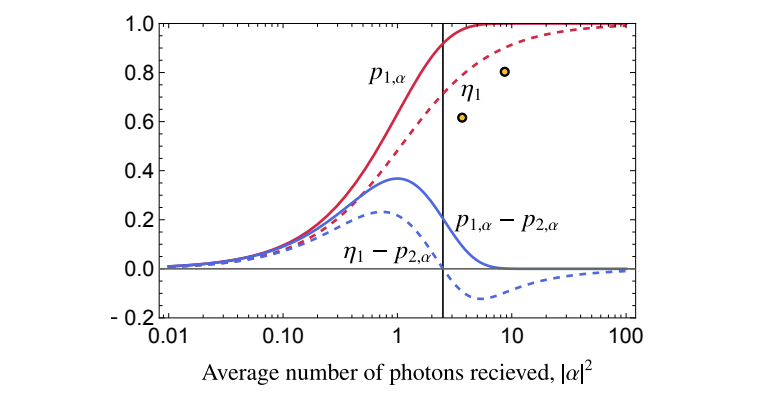
Typical client-server configurations for delegated quantum computing, highlighting the semi-classical channel model used in this work.
What Is Secure Delegated Quantum Computing and Why Does It Matter?
In secure delegated quantum computing, a client asks a remote quantum server to execute a computation on its behalf. The goal is not only to offload the quantum work, but to do so without exposing sensitive information. In the setting studied in this paper, the protocol is designed so that a malicious server or eavesdropper should not learn the client’s data or algorithm, while the client can still test whether the computation was performed as requested.
That matters because quantum computing is likely to be delivered through cloud or service-provider models long before most users ever own a quantum computer. For high-value workloads, that creates an obvious trust problem. If the computation involves sensitive data, proprietary methods, or valuable outputs, privacy and verification are not optional extras- they are part of what makes delegated quantum computing useful in the first place.
Why Existing Secure Delegated Quantum Computing Protocols Are Hard to Implement
The problem is that many existing SDQC protocols are still demanding from a hardware point of view. Information-theoretically secure approaches often require the client to do something genuinely quantum, such as preparing single qubits or measuring them. Other approaches reduce the client’s quantum burden, but then pay the price elsewhere through weaker security assumptions, lack of composability, or significant overhead on the server side.
This paper targets that exact bottleneck. As the authors explain, earlier proposals can also require operations that are especially hard to realize on real hardware, such as isolating single photons from laser pulses, performing polarization-preserving photon-number quantum non-demolition measurements, or relying on demanding photonic entangling operations. The result is a clear gap between elegant security theory and experimentally realistic implementation.
How Semi-Classical Light Reduces the Hardware Cost of Secure Delegated Quantum Computing
The phrase semi-classical light is the key shift in this paper. Instead of asking the client to own a single-qubit source, the protocol lets the client work with attenuated laser pulses; weak coherent states that are far closer to practical optics than a full client-side quantum source. In plain language, the client sends carefully prepared weak laser pulses rather than idealized single photons.
On the server side, a quantum emitter takes over the harder quantum role. The emitter uses the incoming pulse to imprint a rotation on an emitted photonic qubit, so the polarization chosen by the client becomes part of the generated quantum state. In the paper’s own language, the emitter acts as both a “laser-to-qubit converter” and an entanglement generator. That is what makes the architecture especially compelling for photonic implementations.
How Quantum Emitters Enable Blind Graph State Preparation
This dual role of the quantum emitter is one of the most elegant parts of the paper. First, it converts coherent laser pulses into polarization-encoded photonic qubits. Then it entangles successive photons, allowing the server to build the graph-state resources needed for blind and secure delegated quantum computation. Because the emitted photons inherit the client’s hidden polarization angles, the resource state remains encrypted from the server’s point of view.
The practical benefit is just as important as the conceptual one. The server does not need to rely on photon-photon entangling gates for the whole computation. Instead, interacting quantum emitters can generate chains of photonic qubits and create the required structure with far fewer demanding operations. That is a major reason this work feels much closer to realistic photonic hardware than many earlier SDQC proposals.
How Secure Delegated Quantum Computing with Semi-Classical Light Preserves Information-Theoretic Security
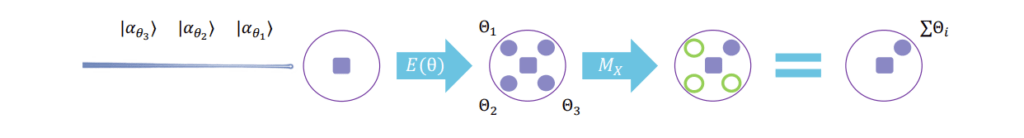
Weak coherent pulses are practical, but they introduce a new problem: they can contain more than one photon, and that extra redundancy can leak information about the client’s secret angle. The paper takes a deliberately pessimistic security view and assumes that multi-photon components may fully leak polarization information. That makes the security challenge sharper, but it also makes the final result more credible.
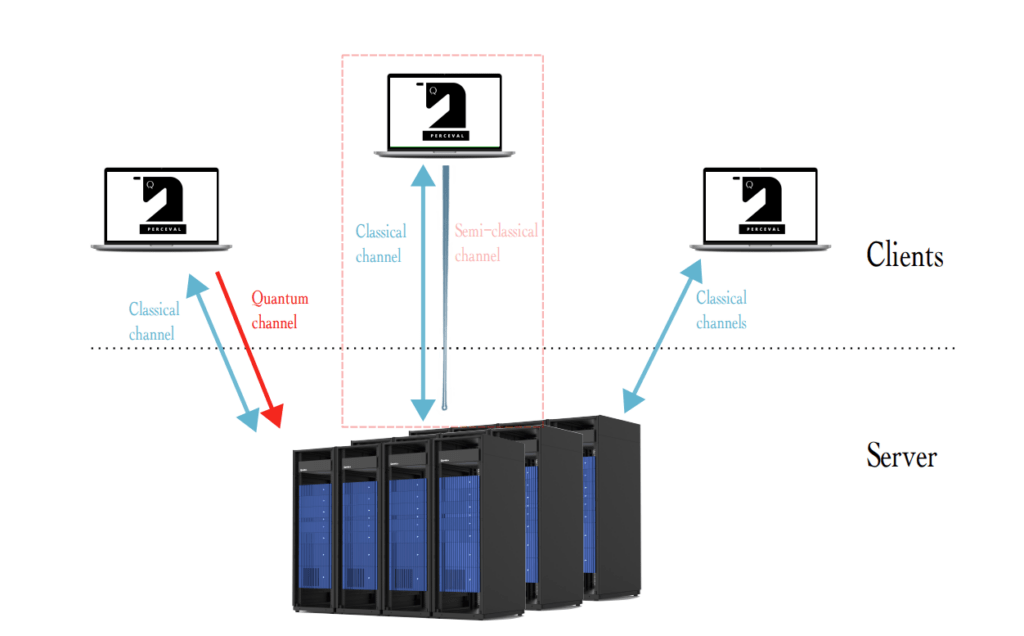
To suppress that leakage, the authors introduce a privacy-amplification gadget based on GHZ-state generation. Alice sends several randomly rotated weak coherent pulses, Bob uses them to drive the quantum emitter, and the hidden angle of the final state becomes the sum of multiple secret rotations. Bob measures all but one of the resulting qubits, and Alice aborts if too few photons were successfully detected. In intuitive terms, the server now has to learn all of the hidden pieces rather than just one, which makes the leakage probability shrink exponentially with the number of pulses used in the gadget.
This is not just a qualitative argument. The paper proves that the blind-state-preparation error decreases exponentially in the number of pulses used in the privacy-amplification step, and then composes that result into full blind and secure delegated protocols within the Abstract Cryptography framework. For the SDQC construction, the resulting security bound combines the new semi-classical-light component with an existing SDQC verification layer, while still tolerating a constant level of honest noise.
GHZ privacy amplification with weak coherent pulses, showing how multiple hidden rotations are combined to suppress information leakage.
How Close Is Practical Secure Delegated Quantum Computing with Semi-Classical Light?
One of the strongest aspects of the paper is that it does not stop at an abstract protocol. It also studies concrete physical schemes for implementation. The main condition for security amplification is that the single-photon generation efficiency must beat the probability of multi-photon leakage. The authors analyze this requirement for a two-level emitter and for alternative emitter structures, including a Lambda-type scheme.
The conclusion is encouraging, but measured. Existing experimental results with weak laser pulses driving quantum dots do not yet meet the full regime needed for security amplification, but the trend is favorable enough that the authors explicitly describe proof-of-concept experiments as feasible with current technology. They also argue that there are no fundamental limitations blocking implementation, even if better excitation schemes, filtering strategies, and hardware designs are still needed.
Implementation analysis showing when security amplification becomes possible and how current experimental data compare with the target regime.
Why This Paper Matters for Photonic Quantum Computing
This paper matters because it narrows the gap between cryptographic security and photonic realism. The client no longer needs a single-qubit source or a single-qubit measurement device. The server does not need to perform some of the most daunting operations often associated with photonic SDQC, such as polarization-preserving photon-number measurements or general photon-photon entangling gates. And yet the protocol still retains information-theoretic composable security.
For photonic quantum computing, that combination is especially important. It shows how quantum emitters and photonic graph-state generation can support not only computation and networking, but also secure delegated computing protocols with realistic experimental pathways. Rather than asking hardware to fit an idealized protocol, the paper redesigns the protocol around hardware that is much closer to what photonic platforms can plausibly deliver.
Conclusion
Towards practical secure delegated quantum computing with semi-classical light gives a strong answer to a long-standing challenge in quantum cloud security: how to keep powerful security guarantees without asking too much from the hardware. By combining weak laser pulses on the client side with quantum emitters on the server side, Quandela researchers show that secure delegated quantum computing can be both cryptographically rigorous and much closer to practical photonic implementation. The next steps are clear — experimental validation, improved leakage models, and better hardware schemes — but the direction is already an important one for photonic quantum security.
FAQ
Does secure delegated quantum computing with semi-classical light remove the need for a single-qubit source?
Yes. In this protocol, the client only needs to manipulate attenuated laser pulses rather than prepare ideal single qubits. That is one of the paper’s main practical advances.
What do quantum emitters do in this secure delegated quantum computing protocol?
They do two jobs at once: they convert the incoming coherent pulses into photonic qubits, and they generate the entanglement needed to build encrypted graph states for blind and secure delegated computation.
Is the protocol already ready for full deployment?
Not yet as a turnkey system. The paper’s implementation analysis is encouraging, and the authors say proof-of-concept experiments may be feasible with current technology, but additional work is still needed on excitation schemes, filtering, and hardware optimization.
References
- Boris Bourdoncle, Pierre-Emmanuel Emeriau, Paul Hilaire, Shane Mansfield, Luka Music, and Stephen Wein. Towards practical secure delegated quantum computing with semi-classical light. Quantum 9, 1943 (2025). arXiv:2409.12103.